Raspberry Pi NAS Project
The Raspberry Pi is a versatile little computer suitable for a wide range of projects. I am currently working on setting up a Network Attached Storage (NAS) system using the Raspberry Pi 5.
Project Overview
haha placeholder text


Components used (click to expand):
Raspberry Pi 5 (8GB)
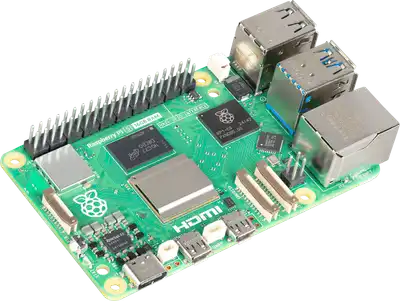
The heart of the project. The Raspberry Pi 5 provides the processing power and connectivity needed for a NAS. I use the official active cooler to keep it cool under load.
4x Samsung 870 EVO 1TB SSD

The gold standard for SSDs. These drives offer excellent performance and reliability for our NAS.
Radxa Penta SATA HAT

This HAT allows you to connect multiple SATA drives to your Raspberry Pi, turning it into a little NAS.
Radxa Penta SATA Top Board

This top board provides cooling for the SATA drives and helps with overall heat dissipation.
22mm M2.5 Standoffs and washers


These standoffs and washers are used to adjust the height of the HAT in order to give more clearance for the active cooler.
Radxa Power DC12 60W

The HAT will get power from the 60W PSU and power the Raspberry Pi through GPIO pins.
Setup the system
1. Download the Raspberry Pi Imager from the official Raspberry Pi website. Prepare a microSD card with OS using the Imager.
2. Initial setup and system update
After the first boot, perform the initial setup:
sudo apt update && sudo apt full-upgrade -y
# For Pi 5, below is not necessary but just in case
sudo rpi-eeprom-update -a
Reboot the system to apply updates:
sudo reboot
Optional: Disable passwordless sudo
# find the file that enables passwordless sudo
sudo grep -i nopasswd /etc/sudoers.d/*
# edit the file to remove the NOPASSWD directive, let's say the file name is 010_pi-nopasswd
sudo visudo -f /etc/sudoers.d/010_pi-nopasswd
Change the line from:
your_account_name ALL=(ALL) NOPASSWD: ALL
to:
your_account_name ALL=(ALL) ALL
- your_account_name → the username this rule applies to
- ALL=(ALL) → it can run commands as any user (not just root)
- ALL → it can run any command
To enable root (Not necessary, just for reference):
sudo passwd root
Switch to root user:
su - root
3. Set up firewall and fail2ban for security:
3.1 Install and configure UFW (Uncomplicated Firewall):
sudo apt install ufw -y
sudo ufw default deny incoming
sudo ufw default allow outgoing
sudo ufw allow ssh
sudo ufw enable
3.2 Set up fail2ban to protect against brute-force attacks:
Install and configure fail2ban:
sudo apt install fail2ban -y
sudo systemctl enable fail2ban
sudo systemctl start fail2ban
We can tune /etc/fail2ban/jail.local for stricter rules (e.g., ban after 3 attempts, longer ban
times).
Example configuration snippet for /etc/fail2ban/jail.local:
[sshd]
enabled = true
port = (your_custom_port)
filter = sshd
logpath = /var/log/auth.log
maxretry = 3
bantime = 1h
To apply changes, restart fail2ban:
sudo systemctl restart fail2ban
5. Remove unnecessary packages and clean up:
Clean up unused packages to free up space:
sudo apt autoremove --purge
4. Enable SSH for remote access:
4.1 Start and enable SSH service:
sudo systemctl enable ssh
sudo systemctl start ssh
4.2 Configure SSH keys for passwordless login *NOT ON Raspberry Pi, run below on main machine*
ssh-keygen -t ed25519
4.2a Linux/Mac:
ssh-copy-id user@hostname_or_ip
4.2b For Windows PowerShell:
type $env:USERPROFILE\.ssh\id_ed25519.pub | ssh -p (port_number) user@hostname_or_ip "mkdir -p ~/.ssh &&
chmod 700 ~/.ssh && cat >> ~/.ssh/authorized_keys && chmod 600 ~/.ssh/authorized_keys"
4.3 Creating a config file for SSH (optional)
In C:\Users\your_user_name\.ssh\config (Windows)
or ~/.ssh/config (Linux/Mac):
Host name_you_want_to_save
HostName hostname_or_ip
User your_username
Port port_number
Now you can simply connect using:
ssh name_you_want_to_save
4.4 Disable password authentication for better security
Edit /etc/ssh/sshd_config on Raspberry Pi:
Include /etc/ssh/sshd_config.d/*.conf
AllowUsers your_username
DenyUsers sambauser // Can do this later after Samba setup
Port 22 // change to your custom port if applicable, 22 is default
PasswordAuthentication no // disable password auth
PermitRootLogin no // disable root login
KbdInteractiveAuthentication no // disable keyboard-interactive auth
UsePAM yes // keep PAM enabled for other auth methods
PubkeyAuthentication yes // ensure pubkey auth is enabled
If you changed the SSH port, allow it through UFW:
sudo ufw allow (your_custom_port)/tcp
4.5 Restart SSH service to apply changes:
sudo systemctl restart ssh
4.6 Allow SSH through UFW if not already done:
- Restrict access with UFW
- Allow SSH only from your subnet:
sudo ufw allow from 192.168.1.0/24 to any port 22
sudo ufw enable
5. Software RAID5 with mdadm.
Enable PCIe interface by editing /boot/firmware/config.txt and add:
dtparam=pciex1
Reboot to apply changes:
sudo reboot
Check if the PCIe device is recognized:
lsblk
lspci
dmesg | grep -i pcie
Install mdadm:
sudo apt update
sudo apt install mdadm -y
Identify drives
lsblk -o NAME,SIZE,TYPE,MOUNTPOINT
Create the RAID 5 array (assuming /dev/sda, /dev/sdb, /dev/sdc, /dev/sdd are the drives):
sudo mdadm --create --verbose /dev/md0 --level=5 --raid-devices=4 /dev/sd[a-d]
Watch the build process:
cat /proc/mdstat
Save the RAID configuration to mdadm.conf:
sudo mdadm --detail --scan | sudo tee -a /etc/mdadm/mdadm.conf
Create a filesystem on the RAID array:
sudo mkfs.ext4 /dev/md0
Create a mount point and mount the RAID array:
sudo mkdir -p /mnt/raid5
sudo mount /dev/md0 /mnt/raid5
To make it permanent, add to /etc/fstab using UUID:
Get the UUID:
sudo blkid /dev/md0
Then add the following line to /etc/fstab:
UUID=(your-uuid) /mnt/raid5 ext4 defaults 0 0
Finally, check with mdstat and mdadm:
cat /proc/mdstat
sudo mdadm --detail /dev/md0
For Debian/Ubuntu systems, update the initramfs to include the RAID configuration:
sudo update-initramfs -u
6. Safe, private Samba setup for file sharing.
Install Samba:
sudo apt update
sudo apt install samba -y
Create a Linux user for Samba:
sudo adduser sambauser
Set a Samba password for the user:
sudo smbpasswd -a sambauser
Edit the Samba configuration file /etc/samba/smb.conf to add a new share:
[AnyNameYouLike]
path = /mnt/raid5
browseable = no
read only = no
valid users = sambauser
Restart Samba service to apply changes:
sudo systemctl restart smbd
DONT FORGET TO ENABLE Samba
sudo systemctl enable smbd
sudo systemctl start smbd
sudo systemctl status smbd
testparm
sudo ufw allow samba
To connect from a Windows machine, use the Run dialog (Win + R) and enter:
\\raspberrypi\AnyNameYouLike
or use the Raspberry Pi's IP address (can check with ip a):
\\192.168.xxx.xxx\AnyNameYouLike
For a fresh setup, we can (optionally) delete the lost+found folder in the share directory to save
space:
ls -la /mnt/raid5/lost+found
# If it is empty, you can remove it
sudo rm -r /mnt/raid5/lost+found
To ensure proper permissions, set the ownership of the share directory to the Samba user:
# Set ownership
sudo chown -R sambauser:sambauser /mnt/raid5
# Set appropriate permissions
sudo chmod -R 755 /mnt/raid5
# 755 gives read, write, execute permissions(7) to the owner, and read and execute permissions(5) to group and others
7. Restrict Samba user access
Set Samba-only user's shell to /usr/sbin/nologin to prevent SSH access
(On some systems, it might be /sbin/nologin):
sudo usermod -s /usr/sbin/nologin sambauser
Test group membership to ensure sambauser is not in any privileged groups
groups sambauser
If sambauser is in any groups like sudo, wheel, adm, or dialout, remove them:
sudo gpasswd -d sambauser sudo
sudo gpasswd -d sambauser wheel
sudo gpasswd -d sambauser adm
sudo gpasswd -d sambauser dialout
Lock down SSH explicitly for sambauser by adding to /etc/ssh/sshd_config:
(Put it right under the Include /etc/ssh/sshd_config.d/*.conf line)
DenyUsers sambauser
Then reload SSH:
sudo systemctl reload ssh
Confirm no sudo access:
sudo -l -U sambauser
It should return "User sambauser is not allowed to run sudo on [hostname]."
To further restrict Samba user access, modify the Samba configuration to disable symlink following:
sudo nano /etc/samba/smb.conf
Add the following lines under the [global] section:
follow symlinks = no
wide links = no
unix extensions = yes
This prevents the Samba user from accessing files outside the shared directory via symlinks.